Fawkes
Wed, 26 Aug 2020 21:27:30 +0200
#^Fawkes


So how do we protect ourselves against unauthorized third parties building facial recognition models that recognize us wherever we may go? Regulations can and will help restrict the use of machine learning by public companies but will have negligible impact on private organizations, individuals, or even other nation states with similar goals.
The SAND Lab at University of Chicago has developed Fawkes1, an algorithm and software tool (running locally on your computer) that gives individuals the ability to limit how unknown third parties can track them by building facial recognition models out of their publicly available photos. At a high level, Fawkes "poisons" models that try to learn what you look like, by putting hidden changes into your photos, and using them as Trojan horses to deliver that poison to any facial recognition models of you. Fawkes takes your personal images and makes tiny, pixel-level changes that are invisible to the human eye, in a process we call image cloaking. You can then use these "cloaked" photos as you normally would, sharing them on social media, sending them to friends, printing them or displaying them on digital devices, the same way you would any other photo. The difference, however, is that if and when someone tries to use these photos to build a facial recognition model, "cloaked" images will teach the model an highly distorted version of what makes you look like you. The cloak effect is not easily detectable by humans or machines and will not cause errors in model training. However, when someone tries to identify you by presenting an unaltered, "uncloaked" image of you (e.g. a photo taken in public) to the model, the model will fail to recognize you.
VAMT
Tue, 25 Aug 2020 20:42:29 +0200
We used a local KMS for M$ Windows Enterprise volume activation. Unfortunately we do not fulfil the required activation thresholds anymore, so we had to switch to MAK activation.
I discovered VAMT from the Windows ADK tools. That is a really handy tool. Overview over your keys and easy mass key changes and activation for all your computers.
#^Use the Volume Activation Management Tool (Windows 10) - Windows Deployment
Well... like most of the time with Micro$oft it sounds nice and good, until you start using it and reach disillusion.
I discovered VAMT from the Windows ADK tools. That is a really handy tool. Overview over your keys and easy mass key changes and activation for all your computers.
#^Use the Volume Activation Management Tool (Windows 10) - Windows Deployment
The Volume Activation Management Tool (VAMT) provides several useful features, including the ability to track and monitor several types of product keys.
Well... like most of the time with Micro$oft it sounds nice and good, until you start using it and reach disillusion.

lightmeter
Fri, 31 Jan 2020 17:38:00 +0100
#^Lightmeter
Funny project. If you look at the code #^https://gitlab.com/lightmeter it is just R
Getting mail reliably and quickly in the inbox of recipients is hard. Lightmeter shows where the bottlenecks are so you don't waste time.
Funny project. If you look at the code #^https://gitlab.com/lightmeter it is just R

Browsh
Thu, 16 Jan 2020 18:22:40 +0100
#^Browsh - A fully interactive, realtime and modern browser rendered to TTY
Browsh is a fully-modern text-based browser. It renders anything that a modern browser can; HTML5, CSS3, JS, video and even WebGL. Its main purpose is to be run on a remote server and accessed via SSH/Mosh or the in-browser HTML service in order to significantly reduce bandwidth and thus both increase browsing speeds and decrease bandwidth costs.
GLPI Inventory Agent for Android
Wed, 08 Jan 2020 17:44:11 +0100
#^glpi-project/android-inventory-agent

GLPI Android Inventory Agent allows your company to maintain control of all mobile devices, whilst providing comprehensive protection and enhanced security for sensitive corporate data, via a centralized management console.
Log file Navigator
Tue, 07 Jan 2020 17:53:06 +0100
nice!!!
#^The Log File Navigator

#^The Log File Navigator

Many logging tools, like Splunk, provide great features but are optimized for large-scale deployments. They require installing and configuring servers before they can be effectively used. There is still a need for a robust log file analyzer for the terminal.
Just point lnav to a directory and it will take care of the rest. File formats are automatically detected and compressed files are unpacked on the fly.
Log files are a wealth of information, lnav can help highlight the parts that are important and filter out the noise.
OBS Studio
Mon, 06 Jan 2020 01:22:51 +0100
Last year someone mentioned OBS Studio  and this weekend I could play a bit with it and it is a really nice and powerful tool. It takes a bit to understand the labels and names, but it is really worth trying it. Actually I only misused it to record a window on the screen. There are tools that are much easier for this task, but it was so much fun to play with all the other features of OBS Studio.
and this weekend I could play a bit with it and it is a really nice and powerful tool. It takes a bit to understand the labels and names, but it is really worth trying it. Actually I only misused it to record a window on the screen. There are tools that are much easier for this task, but it was so much fun to play with all the other features of OBS Studio.  So many sources and such a huge list of streaming destinations it supports out of the box. Too bad I don't stream content, this tool is just too nice not to use it.
So many sources and such a huge list of streaming destinations it supports out of the box. Too bad I don't stream content, this tool is just too nice not to use it.
 and this weekend I could play a bit with it and it is a really nice and powerful tool. It takes a bit to understand the labels and names, but it is really worth trying it. Actually I only misused it to record a window on the screen. There are tools that are much easier for this task, but it was so much fun to play with all the other features of OBS Studio.
and this weekend I could play a bit with it and it is a really nice and powerful tool. It takes a bit to understand the labels and names, but it is really worth trying it. Actually I only misused it to record a window on the screen. There are tools that are much easier for this task, but it was so much fun to play with all the other features of OBS Studio.  So many sources and such a huge list of streaming destinations it supports out of the box. Too bad I don't stream content, this tool is just too nice not to use it.
So many sources and such a huge list of streaming destinations it supports out of the box. Too bad I don't stream content, this tool is just too nice not to use it.
Icinga Director v1.7.0
Mon, 30 Sep 2019 11:01:42 +0200
Finally 
#^Icinga Director v1.7.0 has been released
The first release that includes my property modifier from December last year.

#^Icinga Director v1.7.0 has been released
Over the last four years, the Icinga Director has grown from an optional configuration add-on to a mature Software product with lot‘s of features. Most Icinga installations are now driven by the Director, no matter whether they are small or huge, manually curated or fully automated.
But it will not stop here. Many cool ideas are eager to finally become reality. Director v1.7 is a huge step in that direction, as it lays the foundation for a completely new type of features. We are now able to delegate complex tasks to a dedicated background daemon that has been introduced with this version. New library modules have been published, allowing us to share cool bleeding edge funtionality among different modules in a more efficient way.
The first release that includes my property modifier from December last year.

Open Data nutzen
Mon, 09 Sep 2019 16:02:54 +0200
#^Open Data nutzen: Wie der Refugee Datathon Zahlen zum Thema Asyl verarbeitet - Linux Magazin
Politisch aufgeladene Diskussionen wie die ums Asyl brauchen belastbare Zahlen. Dank des Informationsfreiheitsgesetzes sind diese direkt bei den Behörden erhältlich. Die liefern allerdings oft nur schlecht geeignete Formate. Gefragt sind dann Tools, um sie aufzubereiten.
Wer Zahlenmaterial aus verschiedenen Quellen, verschieden formatiert und mit verschiedenen Größenordnungen verarbeiten muss, braucht die richtige Technik. Dieser Beitrag stellt einen bewährten Ansatz vor und nutzt als Beispiel ein Projekt, zu dem sich 2015 eine Gruppe von Menschen aus der IT zusammenfand, um öffentliche Daten zum Thema Asyl einzufordern und sichtbar zu machen: der Refugee Datathon Munich.
Die Gruppe trifft sich seitdem regelmäßig in ihrer Freizeit, um zu einem Fakten-basierten Verständnis der Flüchtlingssituation beizutragen. Die Autorin dieses Artikels gehört dieser Gruppe an. Wie sieht der Weg von den Behördendaten bis zum Erkenntnisgewinn aus?
Zentrales Logging mit dem Elastic Stack
Fri, 23 Aug 2019 17:25:13 +0200 last edited: Fri, 23 Aug 2019 18:16:09 +0200
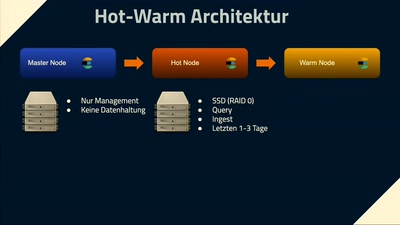
Dezentrales Logging wird mit der steigenden Zahl von zu überwachenden Prozessen immer aufwändiger. Deshalb gibt es seit mehreren Jahren Tools welche das Zentrale Logging unterstützen. In diesem Vortrag soll der Elastic Stack als ein solches Tool vorgestellt werden.
In der Welt der Microservices ist die Anzahl der Logs-produzierenden Prozesse sehr groß und liegt durchaus im Bereich von 100-1000 Prozessen. Eine manuelle Log-Verarbeitung ist hier so gut wie undenkbar. Doch auch monolithische Services laufen oftmals dezentral und das Analysieren der Produktions-Logs ist dann häufig auch mit viel Aufwand verbunden. Mithilfe eines zentralen Loggins lässt sich eine viel bessere Übersicht über den Gesamtzustand eines Systems gewinnen, da nicht jedes Log einzeln untersucht werden muss, sondern die Logs aggregiert und somit auch leicht automatisiert ausgewertet werden können. Der Elastic-Stack bietet die Möglichkeit, große Mengen an Logs zu speichern und zu durchsuchen. Das Ökosystem um den ELK-Stack unterstützt Entwickler, DevOps usw. dabei, die Logs schnell und einfach aufzubereiten, damit diese gut analysierbar sind. In diesem Vortrag werden die Vor- und Nachteile des zentralen Loggins dargelegt und gezeigt, wie sich der Elastic Stack in Umgebungen einbinden lässt.
#ELK #FrOSCon14 #FrOSCon2019
Cheat.sh
Fri, 05 Jul 2019 14:49:20 +0200
#^cheat.sh/:firstpage
To access a cheat sheet you can simply issue a plain HTTP or HTTPS request specifying the topic name in the query URL:
curl cheat.sh/tar
curl #^https://cheat.sh/tar
Elastic SIEM
Wed, 26 Jun 2019 16:51:24 +0200
#^SIEM on the Elastic Stack | Elastic SIEM
Security teams use Elastic SIEM to detect threats by analyzing events from network, host, and cloud technologies, as well as other data sources.
Elastic SIEM equips security practitioners with easy data ingestion via Beats, shareable analytics based on the Elastic Common Schema (ECS), and the ability to interact with security data using the #SIEM app in Kibana. As threats continue to evolve, so too will Elastic SIEM.
CI/CD tools
Fri, 11 Jan 2019 17:45:01 +0100
#^7 CI/CD tools for sysadmins | Opensource.com


An easy guide to the top open source continuous integration, continuous delivery, and continuous deployment tools.
Sharing is Caring
Fri, 21 Dec 2018 11:51:06 +0100
#^MISP » ADMIN Magazine 48/2018

#^MISP - Malware Information Sharing Platform and Threat Sharing - The Open Source Threat Intelligence Platform

Shared Protection By Matthias Wübbeling
The Malware Information Sharing Platform lets you record and document security incidents – and share the information with users on other networks.
Cunning attackers often collaborate with others and share information about vulnerabilities. Companies, on the other hand, face hackers as lone warriors and all too often rely on traditional security technologies. But companies can also share IT security knowledge. One platform for sharing security information is the Malware Information Sharing Platform (MISP).
#^MISP - Malware Information Sharing Platform and Threat Sharing - The Open Source Threat Intelligence Platform
MISP - a threat information sharing platform - The Open Source Threat Intelligence Platform
Lastscrape
Wed, 28 Feb 2018 22:27:56 +0100
This python3 script works really nice to export the last.fm history.
#^encukou/lastscrape-gui

In February 2005 my first scrobble was a Norwegian singer, then an Indonesian song. Around 17800 songs later in November 2014 was my last scrobble to last.fm. Actually I wanted to run my own GNU FM installation then, but unfortunately never finished to set it up.
#^encukou/lastscrape-gui
lastscrape-gui - GUI for getting scrobbles from last.fm and moving them somewhere else
In February 2005 my first scrobble was a Norwegian singer, then an Indonesian song. Around 17800 songs later in November 2014 was my last scrobble to last.fm. Actually I wanted to run my own GNU FM installation then, but unfortunately never finished to set it up.

Retargetable Decompiler
Wed, 20 Dec 2017 20:37:42 +0100
#^Retargetable Decompiler
RetDec is an open-source machine-code decompiler based on LLVM.
The decompiler is not limited to any particular target architecture, operating system, or executable file format:
* Supported file formats: ELF, PE, Mach-O, COFF, AR (archive), Intel HEX, and raw machine code.
* Supported architectures (32b only): Intel x86, ARM, MIPS, PIC32, and PowerPC.
TYPO3 Console: A CLI tool for TYPO3
Fri, 07 Jul 2017 17:40:12 +0200
nice tool when you work with #TYPO3.
TYPO3 Console: Getting things done
TYPO3 Console: Getting things done
The TYPO3 console is a great tool in order to get things done quickly. It provides many commands that will ease your live with TYPO3 a lot. Even if you are not used to command line tools, you should, no, you must have a look at this post.
monitor the progress of data through a pipe
Thu, 22 Jun 2017 23:48:49 +0200
This is a really nice tool I didn't knew something like that exists. How many times I was wondering how the progress of loading a sqldump was.
man pvpv shows the progress of data through a pipeline by giving information such as time elapsed, percentage completed (with progress bar), current throughput rate, total data transferred, and ETA.
To use it, insert it in a pipeline between two processes, with the appropriate options. Its standard input will be passed through to its standard output and progress will be shown on standard error.
This website is tracked using the Piwik analytics tool. If you do not want that your visits are logged this way you can set a cookie to prevent Piwik from tracking further visits of the site (opt-out).